03 August 2022
Microsoft Azure - Identifying and Managing Risk
The Microsoft Azure environment is inherently dynamic, and changes to existing configuration settings and the introduction of new settings by Microsoft are routine. This requires organisations and system administrators to regularly interact with Microsoft Azure to ensure risks are appropriately identified and managed.
Some of the items we commonly identify as issues across Azure environments include logging, monitoring and alerting configuration inconsistencies, limited use of malware protections, limited or no compliance to configured policies, and a lack of data protection on storage accounts.
Available as a one-off service, or as an ongoing incremental service, our Azure Security Review is designed to minimise any risk or uncertainty you might have about the security of your Azure environment and comprises of 3 elements:
1 - Review
- Review customer supplied information
- Conduct interviews with key staff
- Review Azure configuration settings such as every entry and exit point, data aggregation points, overall Azure security configuration and more
2 - Analysis
- Analyse, correlate and collate all information
- Link findings to threat/risk model and develop risk ratings
3 - Reporting
We provide a detailed report which includes –
- An executive summary of the Azure security review, with a risk analysis commentary and security recommendations. Content is written for business people, the executive summary will allow you to discuss how to improve your Azure security posture.
- A detailed “Key Observations” section for the CIO or IT Manager covering our security findings, a risk analysis commentary and our recommendations to improve security posture.
The last section of the report covers feedback on where security best practice is being applied and documents steps for remediation with a commentary on the impact level of those steps.
To discuss this service and the deliverables please contact Mike or Steve.
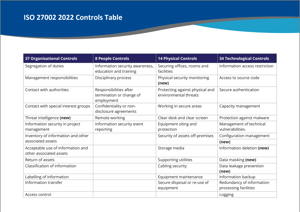
ISO making changes to their guidance
This year there are substantial changes afoot for ISO27002 standards content.
What are those changes?
1) The title of the standard has changed, from ‘Information technology – Security techniques – Code of practice for information security controls’ to ‘Information security, cyber security and privacy protection – Information security controls’. This signifies a key shift from a code of practice to a more reference-style set of controls.
2) There are now 93 controls, down from 114. None of the existing controls have been dropped, instead there’s been a wholesale rearranging and remapping, and there are in fact 11 new controls including titles such as ‘Threat intelligence’, ‘Configuration management’, ‘Information deletion’ and ‘Secure coding’ etc.
3) The controls are now structured across themes and attributes. The themes replace the clauses of old, and they match the control groupings listed in clauses 5–8. The attributes are five subsets attached to each control, and each attribute can be further parsed by type (see brackets):
- Control type (preventive, detective, corrective)
Information security properties (confidentiality, integrity, availability) - Cyber security concepts (identify, protect, detect, respond, recover)
- Operational capabilities (governance, asset management, etc.)
- Security domains (governance and ecosystem, protection, defence, resilience)
View a table of the new ISO controls.
In line with these changes, we will be providing an upgrade for customers with subscriptions to Policy Management as a Service (PMaaS) and valid maintenance for the IT Policy System in due course. More information will be provided to our customers as we complete our integration of ISO 27002:2022.
Watch our video - Policy Management as a Service Indepth.