


25 September 2018
Making cloud computing more secure – the shared responsibility model
Cloud computing continues to attain increasing levels of investment from organisation’s in ANZ. Whilst this model has removed the burden and complexity of having to build and host systems, to assume the cloud environment is secure is flawed.
The objective of the Shared Responsibility Model is to create a secure and compliant computing environment by sharing the security workload. The model addresses the following-
- What is the cloud platform vendor responsible for securing?
- What is the cloud customer organisation responsible for securing?
- Which responsibilities are shared between both parties to create a secure and compliant computing environment?
The 2 graphics below from Microsoft and Amazon provide a good visual representation of the Shared Responsibility Model.
Microsoft’s graphic outlines how responsibilities shift and change as an organisation moves from an on-premise architecture to IaaS, PaaS and SaaS architectures.
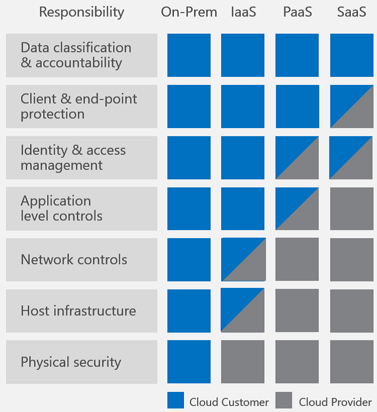
Figure 1: Microsoft Shared Responsibility Model
Amazon’s graphic depicts customer’s responsibilities for security “in” the cloud and AWS’ responsibilities for security “of” the cloud.
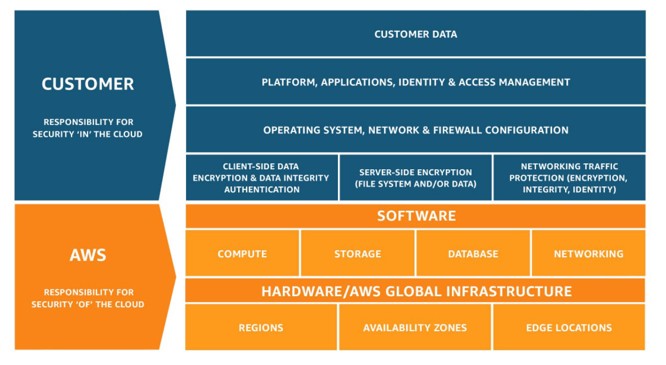
Figure 2: AWS Shared Responsibility Model
Making sure your organisation manages its responsibilities as it moves through the different cloud adoption phases can be a challenge. As an organisation transitions the potential for security issues to occur increases as gaps can open up in policies, processes, procedures and security control set.
RightScale’s State of the Cloud Report for 2018 highlighted the top cloud challenges as being security and spend.
- Security is a challenge for 77 percent of respondents, while 29 percent see it as a significant challenge.
- Managing cloud spend is a challenge for 76 percent of respondents, while a smaller 21 percent see it as a significant challenge.
- Security is the largest issue among cloud beginners, while cost becomes a bigger challenge for intermediate and advanced users.
- Enterprises cite more challenges across the board than SMBs.
View RightScale’s State of the Cloud Report for 2018
Our experts can provide you with support at any stage through your planning and transition to the cloud to ensure your security architecture is correctly defined and implemented. If you have already done much of the transition work, or concluded the exercise, then a cloud security audit is a good way to validate that the right policies, processes, procedures and controls are in place to protect your business.
Office 365 Security Audit Case Study – Horizon Energy
“This engagement and service to ensure our cloud transition was on the right path is just the start for the organisation. We have derived a lot of follow on value from our interaction with Kaon Security” - Kiran Watkins, General Manager Commercial and Technology
We recently assisted Horizon Energy with their Office 365 implementation by conducting an in-depth security audit. View Horizon Energy's case study.
If you would like to arrange a discussion about how to ensure your move to the cloud is secure contact Mike Conboy or Steve Macmillan - t: 09 570 2233
