Microsoft Azure Security Review
Cloud computing provides businesses with the ability to rapidly provision computing resources without having to consider the costs and time involved in building, or selecting, a suitable data centre. Cloud computing also eliminates, or reduces, the need to invest in the provisioning of on-premise software and hardware deployments, or leasing dedicated technology in a traditional data centre.
Microsoft’s successful Azure platform comprises of interoperable cloud computing services that incorporate open-source, standards-based technologies plus proprietary solutions from Microsoft and other technology companies. With Azure a business can instantly provision on demand computing resources with billing based on their resource consumption.
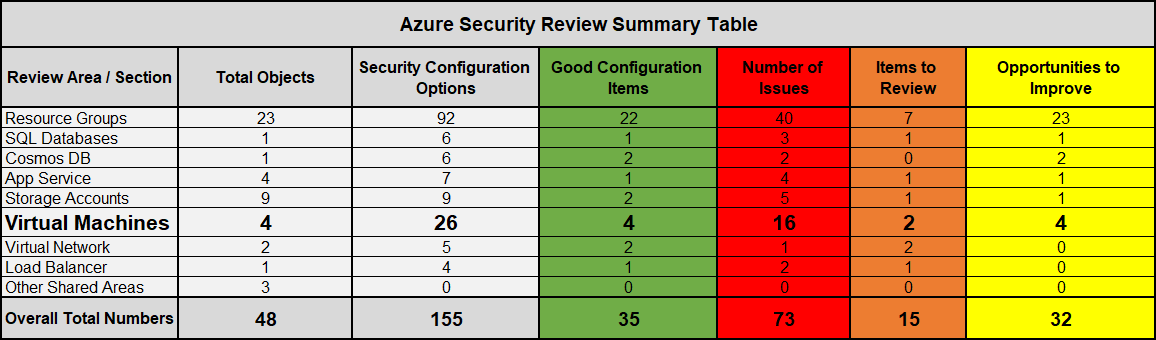
However, when deploying Azure organisations need to make some key security configuration decisions. Making the right decisions can be challenging given the extensive range of configuration options to choose from.
The intricate environment is made up of interlinked virtual machines, storage accounts, application services and databases utilising complex virtual networks and load balancers. Additionally all of these objects are categorised as a Resource within Resource Groups.
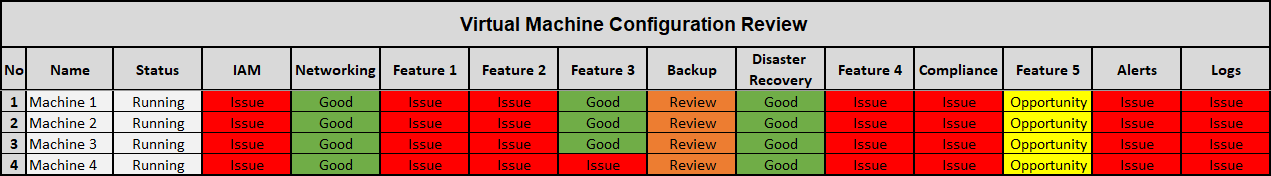
When deploying and configuring Azure infrastructure you will need to consider (for example) different options to manage identity and access controls for using different features, review data resiliency arrangements for protecting information, data recovery in the event of data corruption, determine the best way to prevent data leakage using advanced security capabilities. A “set and forget” approach won’t work as the cloud environment is inherently very dynamic.
The Azure Security Review Service has assisted organisations to improve their IT security posture by optimising their Azure configuration. In delivering this service our experts investigate and assess 8 key areas.
Azure Security Review
Our review process looks to understand how your infrastructure has been architected.
- Some of the areas we investigate and verify include:
- Resource Groups
- Storage Accounts
- Virtual Machines
- Virtual Networks
- Application Services
- SQL database
- Cosmos database
- Load Balancing
Risk Analysis
The adoption of the Microsoft Azure platform introduces new risk considerations for an organisation. Our service will identify the risk considerations associated with Azure resources and data and provide guidance on how to mitigate them.
- Sample list of the areas we investigate and verify include:
- Identity and Access Management
- Compliance
- Networking
- Malware detection
- Storage security
- Logging & Monitoring
Service Overview – 4 Key Elements
- Assess the current configuration and available supporting customer information
- Conduct a risk analysis of the Azure implementation
- Make recommendations to improve the organisational security posture
- Remediation points
Reporting
Kaon Security will provide your organisation with a detailed report which includes:
- An executive summary of the Azure security review, a risk analysis commentary and security recommendations. Specifically written for business people, the executive summary will allow you to discuss how to improve your Azure security posture.
- A detailed “Key Observations” section is provided in the report for the CIO or IT Manager covering our security findings, a risk analysis commentary and recommendations to improve security posture. The supplementary section of the report covers feedback on where security best practise is being applied and documents steps for remediation with a commentary on the impact level of those steps.
Sample Report